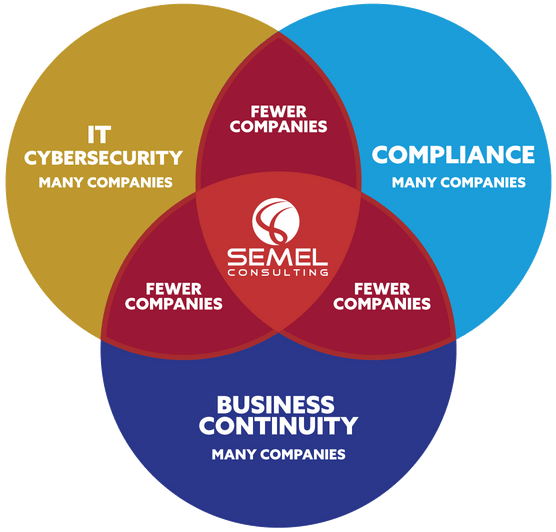
We Take the Risky Trial-and-Error Guesswork out of Cybersecurity, Compliance, and Risk Management, Protecting Your Reputation and Finances
We help smart business owners and executives like you sleep better at night knowing your data is protected, you are compliant with regulations, and your business will survive a disaster or disruption.
click your industry below to see how we can help you:
GET YOUR FREE DISASTER CHECKLIST & BUYER’S GUIDE
Right in the middle of a worldwide pandemic we've seen:
- Hurricane-strength winds - in IOWA!
- The hottest temperature on earth, an unprecedented heat wave, and rolling blackouts - in CALIFORNIA!
- A tropical storm - in MAINE!
ARE YOU PREPARED?
