HIPAA Security Risk Assessment tool has serious flaws
You would think that the US Department of Health and Human Services (HHS) Office of the National Coordinator’s (ONC) would have learned something from the healthcare.gov website fiasco. ONC should have better tested its new HIPAA Risk Assessment tool to avoid the embarrassment of another failed web deployment. Downloads don’t work. ONC automated confusing government language rather than using the opportunity to clearly explain things to really help medical practices. And quality assurance is obviously lacking.
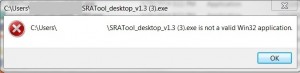
Windows Download
Downloading the Windows version of the HIPAA Security Risk Assessment tool did not work. After over 10 attempts using different web browsers, and hours of downloading time, not once would the entire program download. Only 25% – 50% of the 66mb download completed when it stopped and said the program was ready to run. Clicking on the icon each time resulted in this fatal error.
Rather than the intended review of the Windows tool, we downloaded the iPad version, not the easiest platform to enter lots of data, but at least it worked because it comes from the iTunes store, not a government website.
Easy Download Grade: Fail
Clarity
ONC said it “has ONC has just released a tool that can help make the HIPAA Security Rule more understandable and your security risk assessment easier.” Maybe for some.
Each HIPAA Risk Assessment tool section includes a question, and space to document Current Activities, Notes, and Remediation requirements. You can also document your estimate of the Likelihood and Impact of a threat acting on a vulnerability.
Unfortunately, guidance is provided in the formal and confusing government language used in the Code of Federal Regulations and in guidance from the National Institute of Standards and Technology (NIST.)
Example: Implement a registration process that requires supervisory authorization in order to establish an individual or group identifier. Your practice should prohibit the reuse of information systems account identifiers.
The HIPAA Risk Assessment tool glossary is a good idea but is lacking some obvious definitions. For example, Low and Moderate Impact are defined, but there is no mention of High Impact.
The Contingency Plan definition includes the following incomplete paragraph, demonstrating a lack of quality assurance:
Your practice should develop a detailed continuity of operations plan (COOP) to help recover from major disruptions and resume service for your patients. The Security Rule Contingency Plan standard (
It may have helped to involve writers outside of government because COOP is the name only government organizations use for a Business Continuity Plan.
Electronic Protected Health Information (ePHI) is defined as:
Information that comes within paragraphs (1)(i) or (1)(ii) of the definition of protected health information as specified in this section.
Why confuse people by making them search for the right paragraph when ePHI could simply be defined as something like this?
Identifiable electronic information that relates to an individual’s physical or mental health or the provision of or payment for health care. (Source: OCR)
It might have helped if the HIPAA Security Risk Assessment tool included a description of HIPAA penalties and how they could have been prevented with a good HIPAA Security Risk Assessment.
Clarity Grade: Fail
Value
It is hard to tell if this tool will be successful. First, the Windows download must work before the HIPAA Security Risk Assessment tool will gain a wide audience. Not many will want to manage their Risk Assessment on an iPad.
The goal of a HIPAA Security Risk Assessment is not ‘compliance’ but to protect data.
With its confusing language the HIPAA Security Risk Assessment tool is likely to be a useful reporting tool for compliance professionals but still a challenge for medical practices. By itself the tool does not get to many of the high risk areas we find doing HIPAA Security Risk Assessments for smaller practices, such as the use of consumer-grade equipment that does not secure patient data, personally owned devices, a lack of training and awareness to prevent cybersecurity incidents, and a lack of truly understanding where ePHI is stored and how it moves within, and in and out of, a practice.
True protection of data requires a working knowledge of IT security which is often lacking in smaller health practices. While the HIPAA Security Risk Assessment tool is a good idea, trying to teach health care practices to do their own HIPAA Security Risk Assessment is like teaching IT security professionals to do their own medical checkups. There may be things that they can do themselves, but the results could be disastrous because of the medical knowledge and experience they lack, and the lack of diagnostic tools to identify critical issues.
Perhaps the best guidance comes from the ONC is still from the Top 10 Myths of Security Risk Analysis, “doing a thorough and professional risk analysis that will stand up to a compliance review will require expert knowledge that could be obtained through services of an experienced outside professional.”
Value Grade: Incomplete
originally written for 4MedApproved
